Desert Postcard
Lord of the Tar Lake
The Factory
Not gonna lie, the free PS5 upgrade for Hellblade: Senua’s Sacrifice is really making me want to re-experience that story.
So mind-blowing when I played it years ago.
How could it possibly be any better.
I am so fucking bored of hearing about, and seeing the “fruits” of, AI.
Back to the Plate Gate
Monorail at night
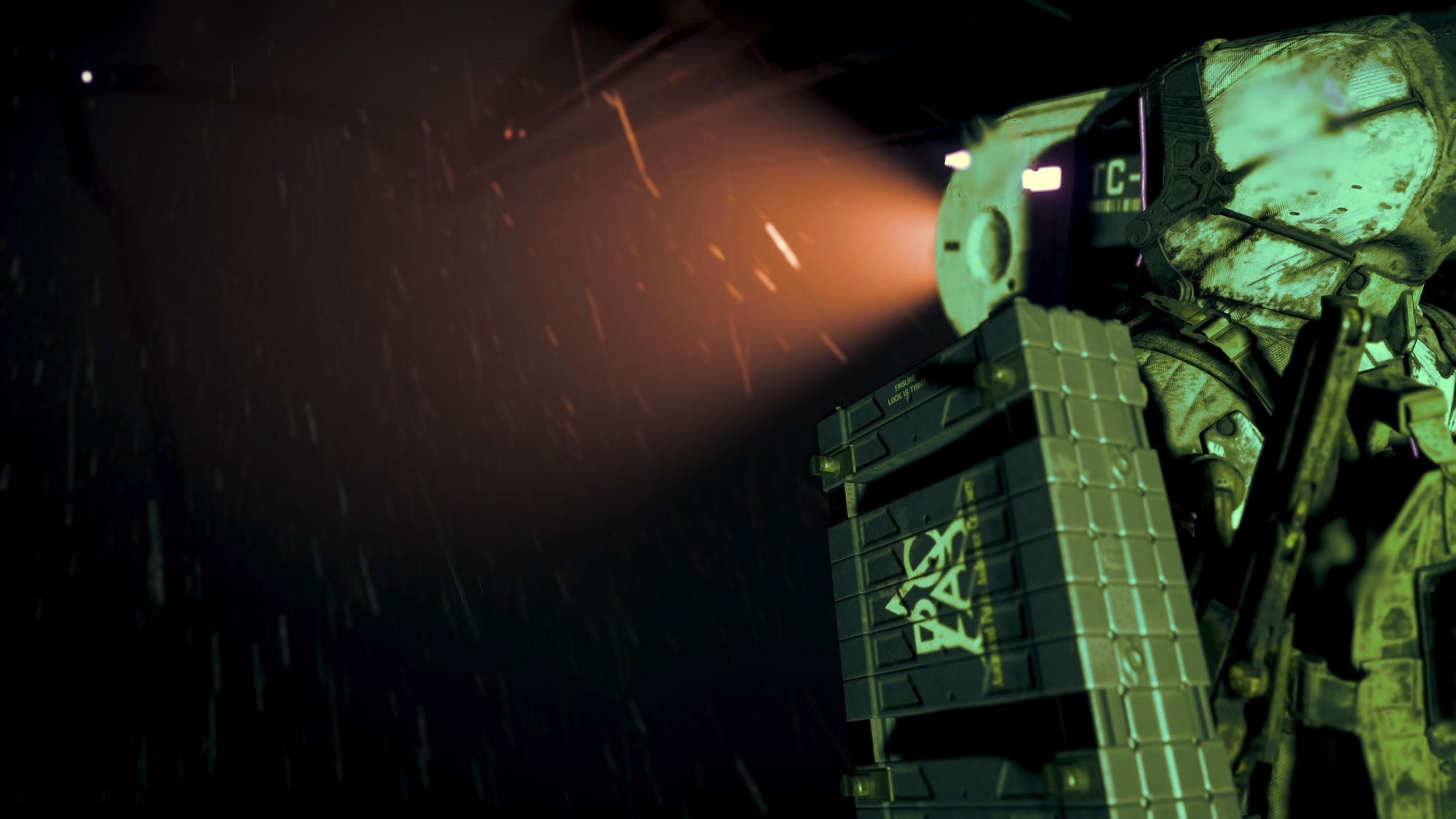
Sam traverses the snowy peaks
The moon is out
The Walking Dead : The Ones who live

The Ones who live has immediately gone up as one of my favourite series in The Walking Dead universe.
Top spot of course is Negan’s introduction. Holy Christ that was intense.
But I gotta say that after finishing the six-episode series of this Rick and Michone spin-off, it has catapulted up to near the top.
And it was a single moment that solidified it for me.
Now I always enjoyed watching Rick grow increasingly capable and deadly as the series moved forward.
I was lucky to start watching The Walking Dead when series three was just coming out, so I didn’t have too much catching up to do.
And it also meant that I’ve been able to see the characters grow steadily over the years, including Rick’s son, Carl.
So when the scene in episode four “What We” came on, where Rick opens up about Carl and the effect that his few years imprisonment has done to his memory of Carl, it destroyed me.
I’ve always been easily triggered by these sorts of emotional scenes. However, since having children of my own recently, it’s basically changed how I see pretty much every thing.
Everything has an additional dimension to it now, it seems.
And the fact that in that scene’s flashback, Carl is shown as being of toddler age — the same as my son — honestly it couldn’t have cut any deeper for me in the world of The Walking Dead.